Home / Capabilities
Modernize How Work Gets Done - One Interface at a Time
From operator dashboards to field technician apps, we develop purpose-built interfaces that transform digital twin & IoT data into actionable insights.
Choose the Best Mobile App Development Approach
Platform-specific App

Cross-platform App
Built for Operational Reality
Built for Operational Reality
Our applications are designed for the environments where work actually happens on production floors, in airport terminals, maintenance facilities, port yards, energy plants, and distributed field locations. Every screen, behavior, and interaction supports clarity, speed, and operational precision.
App Development Challenges We Solve
Apps that look good but don’t support real tasks
We surface real-time data from IoT & digital twins
Interfaces too complex for field conditions
We reduce task time with optimized journeys
High click density & cognitive load
We prioritize clarity and operational decision-making
Frontends disconnected from operational data
We work offline for remote sites and constrained networks
Apps that break in low-connectivity environments
We adapt to specific roles and permission levels
Tools that aren’t role-based and require heavy training
We fit naturally into the existing workflows - not against them
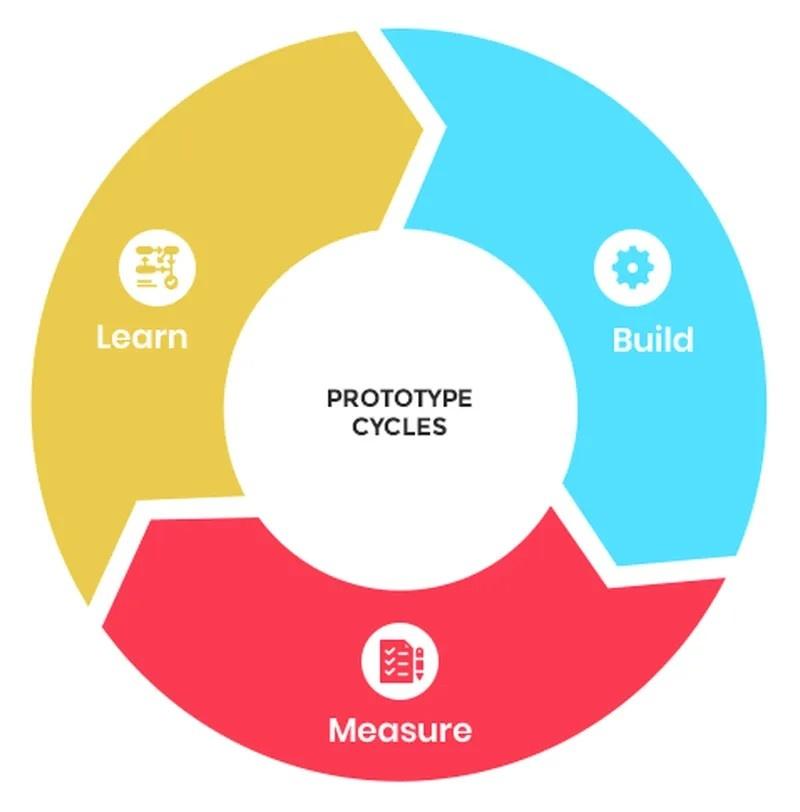
Mobile App Development Lifecycle
The stages covered in the application lifecycle support your business needs in the enterprise-level quality, from new app development to post-launch maintenance.
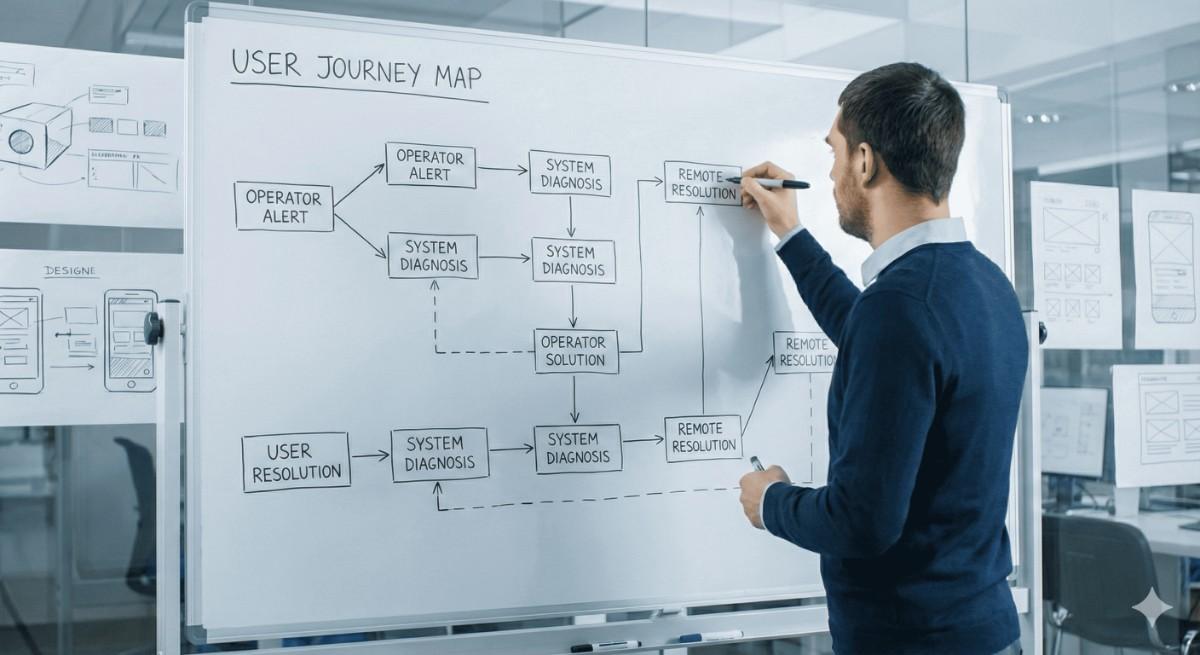
Know MoreProper study of real workflows, environment constraints, user roles, and task frequency, so that the application is built around the actual operational context.
Map real workflows & task patterns
Define role-based user journeys
Identify real-time data connections
Specify functional & reliability needs
Plan scalability & upgrade paths
Built for secure access, fast performance, and resilient data flow.
Support for varied environments & device contexts
Offline-first resilience under weak connectivity
Fast, intuitive navigation models
Layered architecture for maintainability
Built-in security & access controls
Workflow validation carried out at the right time: before development, not after.
Validate workflows before development starts
Expose usability issues early
Confirm clarity & task flow under real conditions
Involve stakeholders in rapid iteration
Align expectations with tangible interaction models
User interfaces crafted for clarity, speed, and field usability. With minimal interaction steps and safety-aware layouts.
Minimal cognitive load for fast decisions
Clear, shallow navigation
Task-focused visual priority
Consistent layouts across roles
Familiar interaction patterns
Reliability assured through repeatable automated checks.
Validate critical workflows automatically
Ensure consistent performance at scale
Test offline behaviour & sync recovery
Security and access testing
Continuous regression checks
Control rollout assured with continuous improvement and stability monitoring.
Controlled rollout with staged deployments
Real-time usage & failure monitoring
User onboarding & adoption support
Feedback-driven refinements
Versioning with rollback safety
Equip Your Workforce With Tools Built For Their Reality
Interfaces We Build
Operator dashboards
Centralized platform for real-time operational monitoring.
Field/maintenance technician mobile apps
Mobile tools for efficient field service and maintenance tasks.
Equipment control & monitoring interfaces
Interfaces for tracking and managing equipment performance.
Energy & portfolio cockpit views
Visualize energy data and portfolio performance in real-time.
Customer & stakeholder portals
Secure access to data and updates for customers and stakeholders.
Asset data tools
Tools for managing and analyzing asset performance and lifecycle.
Analytics data tools
Advanced tools for collecting and analyzing business performance data.
Site inspection & progress dashboards
Real-time insights into site inspections and project progress.
UX for industrial users
Task-time reduction
Reduces required task time
For high-pressure environments
Lorem Ipsum has been the industry's standard dummy text ever since the 1500s
Offline-first readiness
Offline accessibility enabled
Clear visual hierarchy under fast decision contexts
Under fast decision contexts
Touch-friendly controls
User-friendly touch controls
Layouts & permission views
Set for specific roles
Minimal training requirements
Low training is required
Our technical stack & integration fit
We are an app development company engineered for operational reliability - not a consumer-facing mobile dev shop. We deliver applications that integrate seamlessly into enterprise ecosystems using:
Web + Flutter mobile
Develop responsive apps for both web and mobile using Flutter, ensuring a consistent experience across platforms with fast, native performance.
Node.js / Go / Python backends
Build scalable, efficient backends with Node.js, Go, and Python, ensuring high performance, flexibility, and robust support for complex applications.
API-first connectivity
Prioritize API-driven development, enabling seamless integration, modularity, and easy communication between systems for smoother data exchange.
Secure authentication (SSO / AD / LDAP)
Implement secure authentication protocols like SSO, AD, and LDAP to ensure safe, streamlined access management for users across enterprise systems.
Strong encryption and data security
Ensure data protection with industry-standard encryption techniques, safeguarding sensitive information against potential breaches or unauthorized access.
Tight interoperability
Enable seamless communication between applications, digital twin systems, and IoT platforms, enhancing real-time monitoring and control capabilities.
Real-world proof: Unilode global mobility platform
These are applications built to be used — not just to be presented.
Supporting 800+ operational staff
Scalable solutions to support large teams, ensuring smooth operations across diverse roles.
Offline capability for airport zones
Enable seamless operations even in offline environments, crucial for remote airport zones.
Role-tailored task workflows
Custom workflows for different roles, ensuring tasks are streamlined and efficiently managed.
Fast execution for time-sensitive activities
Optimized processes for rapid execution, ensuring timely completion of critical tasks.
Integrated with backend asset intelligence
Real-time integration with asset intelligence systems for accurate data and informed decision-making.
Deployed at scale for high-availability architecture
Ensures system reliability and uptime, even at large-scale deployments with demanding needs.
We Understand How Work Really Gets Done
We are not a generic outsourcing app development company — we are a partner that understands industrial environments, operational workflows, and the nature of real-time decision systems.
Turn Data, Workflow, and UI into Business Advantage
Enable faster decisions, better workflows, and real-time visibility across operational environments.
Testimonials

I believe that Toobler provided me the highest level of communication & coding during my product development. The world has greatly benefited from hands of their innovative team!

Lee Barrett
Founder, Shopbox UK
My experiences with the Toobler folks has been stellar. Their programming has been solid and their designs have been exceptional – a rare commodity in the outsourcing world. Without any hesitation – I will continue to use Toobler on all my projects.

Dave Backman
Founder of movingpermits
Working with Toobler was easy for me. Their staff were always online when I needed to discuss something and they were professional and pleasant in their manner. They were also very knowledgeable and always had a good grasp on what was needed. This is a good company to have in your address book.

Roshan
Project Manager, Heart Ocean