Home / Capabilities
Secure Enterprise, Uninterrupted Business Continuity
Reduce breach risk, eliminate security blindspots, simplify compliance, improve governance, and maintain uptime across all critical systems - even under threat.
How We Strengthen Your Security Posture?
Security compliance solutions isn’t something we bolt on - it’s embedded into every part of your digital ecosystem.
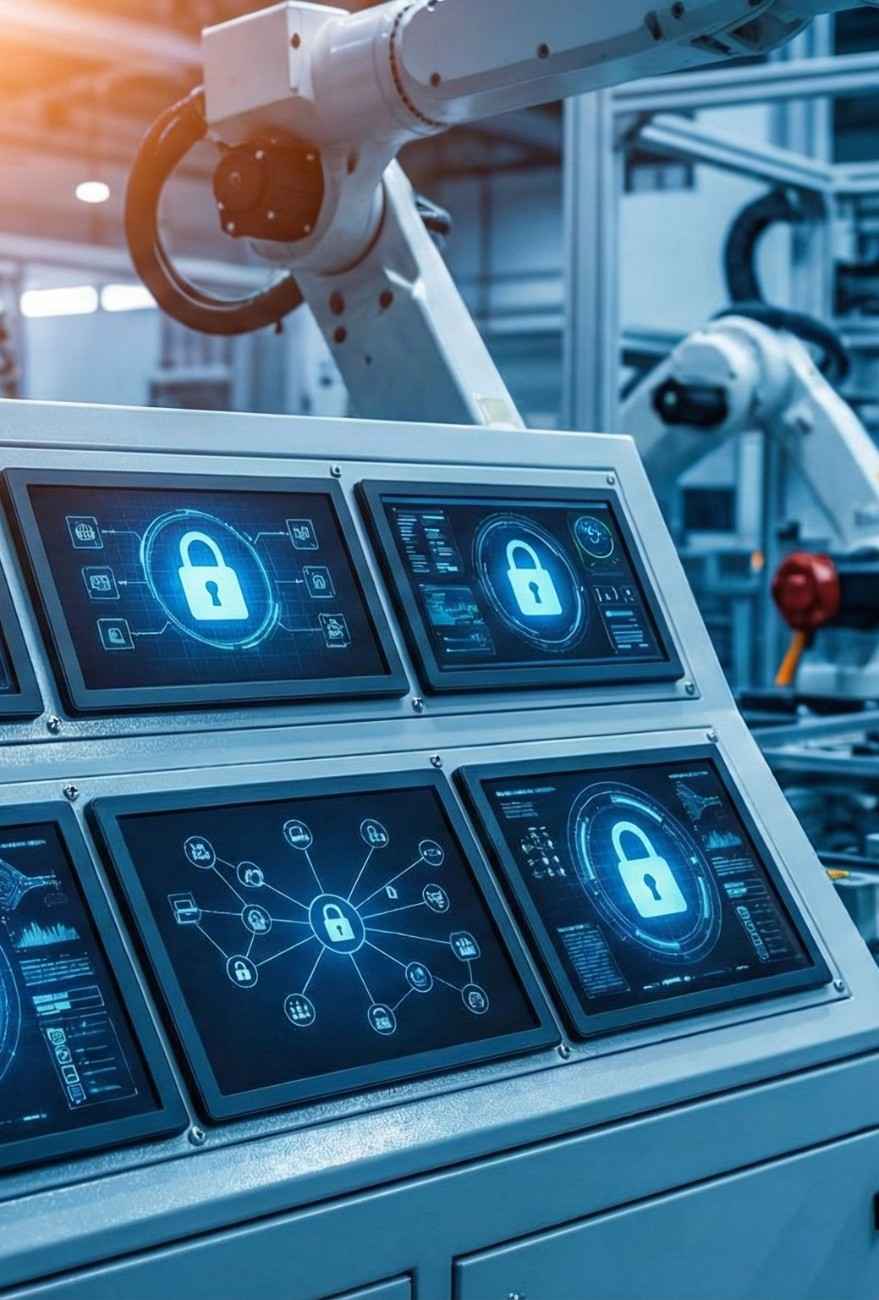
Secured Industrial Data
Protect critical industrial and operational data across diverse environments with robust encryption and security measures to ensure confidentiality and integrity.
Layered Attack Protection
Utilize multi-layered security protocols to minimize vulnerabilities, safeguard against threats, and ensure robust defenses against attacks.
Governance Across Environments
Implement governance controls across on-prem, cloud, and edge environments to maintain consistent compliance, data access, and security.
Compliance-Driven Infrastructure
Align infrastructure with global and industry compliance standards to ensure secure environments and mitigate operational risks.
Secure-By-Design Implementation
We don’t “patch in” security compliance solutions; we architect it from day one.
1
Threat modeling before development
Identify potential threats early to guide secure development.
2
Secure coding practices
Implement best practices for writing secure, resilient code.
3
Continuous vulnerability scanning
Ongoing scanning to detect vulnerabilities in real-time.
4
Regular penetration testing and remediation cycles
Regular tests to find and fix security weaknesses proactively.
Security Services We Deliver
We provide a comprehensive suite of security services that safeguard your data, assets, and systems. From identity management to encrypted data pathways, our solutions ensure robust protection across all environments.
We build identity models that reflect how your organization actually operates:
RBAC mapped directly into AD/LDAP
Permission models aligned with operational hierarchies
Least-privilege enforcement across users, assets, teams, and systems
Your access policies become scalable, auditable, and extremely controlled.
We ensure that your data is secure everywhere, not just at rest or in certain locations:
Encryption in transit and at rest
Key management with strict control policies
Protected data pathways across IoT devices, digital twins, analytics pipelines, and cloud storage environments
Your data is protected across its full lifecycle.
For environments serving multiple operating entities or business units:
Isolated data boundaries
Logical separation policies
Prevention of cross-tenant leakage by default
Your operations remain secure even in complex multi-stakeholder environments.
Edge is where real-world data first enters the system, and where threats often begin:
Hardened edge deployments
Encrypted data ingestion from field devices
Network-level threat filtering
We extend full security control all the way to your physical assets.
How We Partner With You?

Security Assessment
We evaluate your existing systems against compliance and operational requirements.

Architecture & Control Planning
We design IAM models, encryption strategies, and data-control frameworks.

Deployment & Reinforcement
We implement, configure, and lock down your security posture.

Monitoring & Continuous Compliance
We ensure persistence of security with audits, reviews, and lifecycle management.
Build an established, hardened, and resilient foundation for your enterprise!
Trusted Partner for Enterprise-Grade Security
Testimonials

I believe that Toobler provided me the highest level of communication & coding during my product development. The world has greatly benefited from hands of their innovative team!

Lee Barrett
Founder, Shopbox UK
My experiences with the Toobler folks has been stellar. Their programming has been solid and their designs have been exceptional – a rare commodity in the outsourcing world. Without any hesitation – I will continue to use Toobler on all my projects.

Dave Backman
Founder of movingpermits
Working with Toobler was easy for me. Their staff were always online when I needed to discuss something and they were professional and pleasant in their manner. They were also very knowledgeable and always had a good grasp on what was needed. This is a good company to have in your address book.

Roshan
Project Manager, Heart Ocean